The Code Book (41 page)

With Ventris’s deciphering skills and Chadwick’s expertise in Greek, the duo went on to convince the rest of the world that Linear B is indeed Greek. The rate of translation accelerated as each day passed. In Chadwick’s account of their work,
The Decipherment of Linear B
, he writes:
Cryptography is a science of deduction and controlled experiment; hypotheses are formed, tested and often discarded. But the residue which passes the test grows until finally there comes a point when the experimenter feels solid ground beneath his feet: his hypotheses cohere, and fragments of sense emerge from their camouflage. The code “breaks.” Perhaps this is best defined as the point when the likely leads appear faster than they can be followed up. It is like the initiation of a chain reaction in atomic physics; once the critical threshold is passed, the reaction propagates itself.
It was not long before they were able to demonstrate their mastery of the script by writing short notes to each other in Linear B.
An informal test for the accuracy of a decipherment is the number of gods in the text. In the past, those who were on the wrong track would, not surprisingly, generate nonsensical words, which would be explained away as being the names of hitherto unknown deities. However, Chadwick and Ventris claimed only four divine names, all of which were well-established gods.
In 1953, confident of their analysis, they wrote up their work in a paper, modestly entitled “Evidence for Greek Dialect in the Mycenaean Archives,” which was published in
The Journal of Hellenic Studies
. Thereafter, archaeologists around the world began to realize that they were witnessing a revolution. In a letter to Ventris, the German scholar Ernst Sittig summarized the mood of the academic community: “I repeat: your demonstrations are cryptographically the most interesting I have yet heard of, and are really fascinating. If you are right, the methods of the archaeology, ethnology, history and philology of the last fifty years are reduced
ad absurdum.”
The Linear B tablets contradicted almost everything that had been claimed by Sir Arthur Evans and his generation. First of all was the simple fact that Linear B was Greek. Second, if the Minoans on Crete wrote Greek and presumably spoke Greek, this would force archaeologists to reconsider their views of Minoan history. It now seemed that the dominant force in the region was Mycenae, and Minoan Crete was a lesser state whose people spoke the language of their more powerful neighbors. However, there is evidence that, before 1450
B.C
., Minoa was a truly independent state with its own language. It was in around 1450
B.C
. that Linear B replaced Linear A, and although the two scripts look very similar, nobody has yet deciphered Linear A. Linear A therefore probably represents a distinctly different language from Linear B. It seems likely that in roughly 1450
B.C
. the Mycenaeans conquered the Minoans, imposed their own language, and transformed Linear A into Linear B so that it functioned as a script for Greek.
As well as clarifying the broad historical picture, the decipherment of Linear B also fills in some detail. For example, excavations at Pylos have failed to uncover any precious objects in the lavish palace, which was ultimately destroyed by fire. This has led to the suspicion that the palace was deliberately torched by invaders, who first stripped it of valuables. Although the Linear B tablets at Pylos do not specifically describe such an attack, they do hint at preparations for an invasion. One tablet describes the setting up of a special military unit to protect the coast, while another describes the commandeering of bronze ornaments for converting into spearheads. A third tablet, untidier than the other two, describes a particularly elaborate temple ritual, possibly involving human sacrifice. Most Linear B tablets are neatly laid out, implying that scribes would begin with a rough draft which would later be destroyed. The untidy tablet has large gaps, half-empty lines and text that spills over to the other side. One possible explanation is that the tablet recorded a bid to invoke divine intervention in the face of an invasion, but before the tablet could be redrafted the palace was overrun.
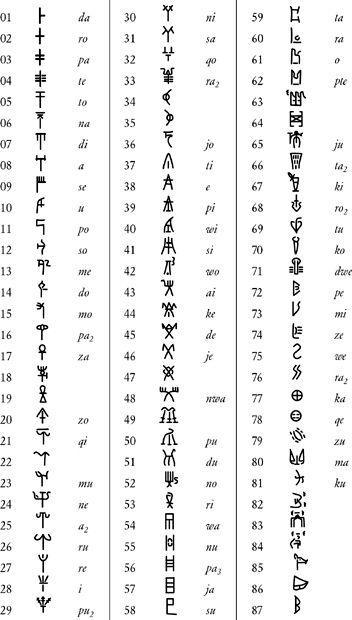
Table 23
Linear B signs with their numbers and sound values.
The bulk of Linear B tablets are inventories, and as such they describe everyday transactions. They indicate the existence of a bureaucracy to rival any in history, with tablets recording details of manufactured goods and agricultural produce. Chadwick likened the archive of tablets to the Domesday Book, and Professor Denys Page described the level of detail thus: “Sheep may be counted up to a glittering total of twenty-five thousand; but there is still purpose to be served by recording the fact that
one
animal was contributed by Komawens … One would suppose that not a seed could be sown, not a gram of bronze worked, not a cloth woven, not a goat reared or a hog fattened, without the filling of a form in the Royal Palace.” These palace records might seem mundane, but they are inherently romantic because they are so intimately associated with the
Odyssey
and
Iliad
. While scribes in Knossos and Pylos recorded their daily transactions, the Trojan War was being fought. The language of Linear B is the language of Odysseus.
On June 24, 1953, Ventris gave a public lecture outlining the decipherment of Linear B. The following day it was reported in
The Times
, next to a comment on the recent conquest of Everest. This led to Ventris and Chadwick’s achievement being known as the “Everest of Greek Archaeology.” The following year, the men decided to write an authoritative three-volume account of their work which would include a description of the decipherment, a detailed analysis of three hundred tablets, a dictionary of 630 Mycenaean words and a list of sound values for nearly all Linear B signs, as given in
Table 23
.
Documents in Mycenaean Greek
was completed in the summer of 1955, and was ready for publication in the autumn of 1956. However, a few weeks before printing, on September 6, 1956, Michael Ventris was killed. While driving home late at night on the Great North Road near Hatfield, his car collided with a truck. John Chadwick paid tribute to his colleague, a man who matched the genius of Champollion, and who also died at a tragically young age: “The work he did lives, and his name will be remembered so long as the ancient Greek language and civilization are studied.”
6 Alice and Bob Go Public
During the Second World War, British codebreakers had the upper hand over German codemakers, mainly because the men and women at Bletchley Park, following the lead of the Poles, developed some of the earliest codebreaking technology. In addition to Turing’s bombes, which were used to crack the Enigma cipher, the British also invented another codebreaking device, Colossus, to combat an even stronger form of encryption, namely the German Lorenz cipher. Of the two types of codebreaking machine, it was Colossus that would determine the development of cryptography during the latter half of the twentieth century.
The Lorenz cipher was used to encrypt communications between Hitler and his generals. The encryption was performed by the Lorenz SZ40 machine, which operated in a similar way to the Enigma machine, but the Lorenz was far more complicated, and it provided the Bletchley codebreakers with an even greater challenge. However, two of Bletchley’s codebreakers, John Tiltman and Bill Tutte, discovered a weakness in the way that the Lorenz cipher was used, a flaw that Bletchley could exploit and thereby read Hitler’s messages.
Breaking the Lorenz cipher required a mixture of searching, matching, statistical analysis and careful judgment, all of which was beyond the technical abilities of the bombes. The bombes were able to carry out a specific task at high speed, but they were not flexible enough to deal with the subtleties of Lorenz. Lorenz-encrypted messages had to be broken by hand, which took weeks of painstaking effort, by which time the messages were largely out of date. Eventually, Max Newman, a Bletchley mathematician, came up with a way to mechanize the cryptanalysis of the Lorenz cipher. Drawing heavily on Alan Turing’s concept of the universal machine, Newman designed a machine that was capable of adapting itself to different problems, what we today would call a programmable computer.
Implementing Newman’s design was deemed technically impossible, so Bletchley’s senior officials shelved the project. Fortunately, Tommy Flowers, an engineer who had taken part in discussions about Newman’s design, decided to ignore Bletchley’s skepticism, and went ahead with building the machine. At the Post Office’s research center at Dollis Hill, North London, Flowers took Newman’s blueprint and spent ten months turning it into the Colossus machine, which he delivered to Bletchley Park on December 8, 1943. It consisted of 1,500 electronic valves, which were considerably faster than the sluggish electromechanical relay switches used in the bombes. But more important than Colossus’s speed was the fact that it was programmable. It was this fact that made Colossus the precursor to the modern digital computer.
Colossus, as with everything else at Bletchley Park, was destroyed after the war, and those who worked on it were forbidden to talk about it. When Tommy Flowers was ordered to dispose of the Colossus blueprints, he obediently took them down to the boiler room and burned them. The plans for the world’s first computer were lost forever. This secrecy meant that other scientists gained the credit for the invention of the computer. In 1945, J. Presper Eckert and John W. Mauchly of the University of Pennsylvania completed ENIAC (Electronic Numerical Integrator And Calculator), consisting of 18,000 electronic valves, capable of performing 5,000 calculations per second. For decades, ENIAC, not Colossus, was considered the mother of all computers.
Having contributed to the birth of the modern computer, cryptanalysts continued after the war to develop and employ computer technology in order to break all sorts of ciphers. They could now exploit the speed and flexibility of programmable computers to search through all possible keys until the correct one was found. In due course, the cryptographers began to fight back, exploiting the power of computers to create increasingly complex ciphers. In short, the computer played a crucial role in the postwar battle between codemakers and codebreakers.
Using a computer to encipher a message is, to a large extent, very similar to traditional forms of encryption. Indeed, there are only three significant differences between computer encryption and the sort of mechanical encryption that was the basis for ciphers like Enigma. The first difference is that a mechanical cipher machine is limited by what can be practically built, whereas a computer can mimic a hypothetical cipher machine of immense complexity. For example, a computer could be programmed to mimic the action of a hundred scramblers, some spinning clockwise, some anticlockwise, some vanishing after every tenth letter, others rotating faster and faster as encryption progresses. Such a mechanical machine would be practically impossible to build, but its “virtual” computerized equivalent would deliver a highly secure cipher.
The second difference is simply a matter of speed. Electronics can operate far more quickly than mechanical scramblers: a computer programmed to mimic the Enigma cipher could encipher a lengthy message in an instant. Alternatively, a computer programmed to perform a vastly more complex form of encryption could still accomplish the task within a reasonable time.
The third, and perhaps most significant, difference is that a computer scrambles numbers rather than letters of the alphabet. Computers deal only in binary numbers-sequences of ones and zeros known as
binary digits
, or
bits
for short. Before encryption, any message must therefore be converted into binary digits. This conversion can be performed according to various protocols, such as the American Standard Code for Information Interchange, known familiarly by the acronym ASCII, pronounced “asskey.” ASCII assigns a 7-digit binary number to each letter of the alphabet. For the time being, it is sufficient to think of a binary number as merely a pattern of ones and zeros that uniquely identifies each letter (
Table 24
), just as Morse code identifies each letter with a unique series of dots and dashes. There are 128 (2
7
) ways to arrange a combination of 7 binary digits, so ASCII can identify up to 128 distinct characters. This allows plenty of room to define all the lowercase letters (e.g., a = 1100001), all necessary punctuation (e.g., ! = 0100001), as well as other symbols (e.g., & = 0100110). Once the message has been converted into binary, encryption can begin.
Even though we are dealing with computers and numbers, and not machines and letters, the encryption still proceeds by the age-old principles of substitution and transposition, in which elements of the message are substituted for other elements, or their positions are switched, or both. Every encipherment, no matter how complex, can be broken down into combinations of these simple operations. The following two examples demonstrate the essential simplicity of computer encipherment by showing how a computer might perform an elementary substitution cipher and an elementary transposition cipher.